Measuring Entitlement Risk: The Time Dimension
In today's digital landscape, managing entitlements effectively is crucial for minimizing security risks. Traditional access management grants users 24/7 access to resources regardless of actual usage patterns. This approach creates significant, but often overlooked, security exposure. Measuring the time dimension of entitlements can transform our understanding of risk and just-in-time (JIT) access can dramatically reduce this exposure.
The hidden risk of continuous access
When we grant an employee access to a system, we're typically providing them with 24/7/365 availability—a total of 8,760 hours per year. But ask yourself: how many of those hours does that employee actually need or use?
The reality is stark: most users only require access for a tiny fraction of those hours. The remaining time represents pure risk exposure with no business benefit. For example:
- An administrator who performs weekly maintenance might only need access for 2 hours per week (104 hours annually)
- A financial analyst accessing financial data might require 20 hours per month (240 hours annually)
- A developer who occasionally troubleshoots production issues might need just 50 hours per year
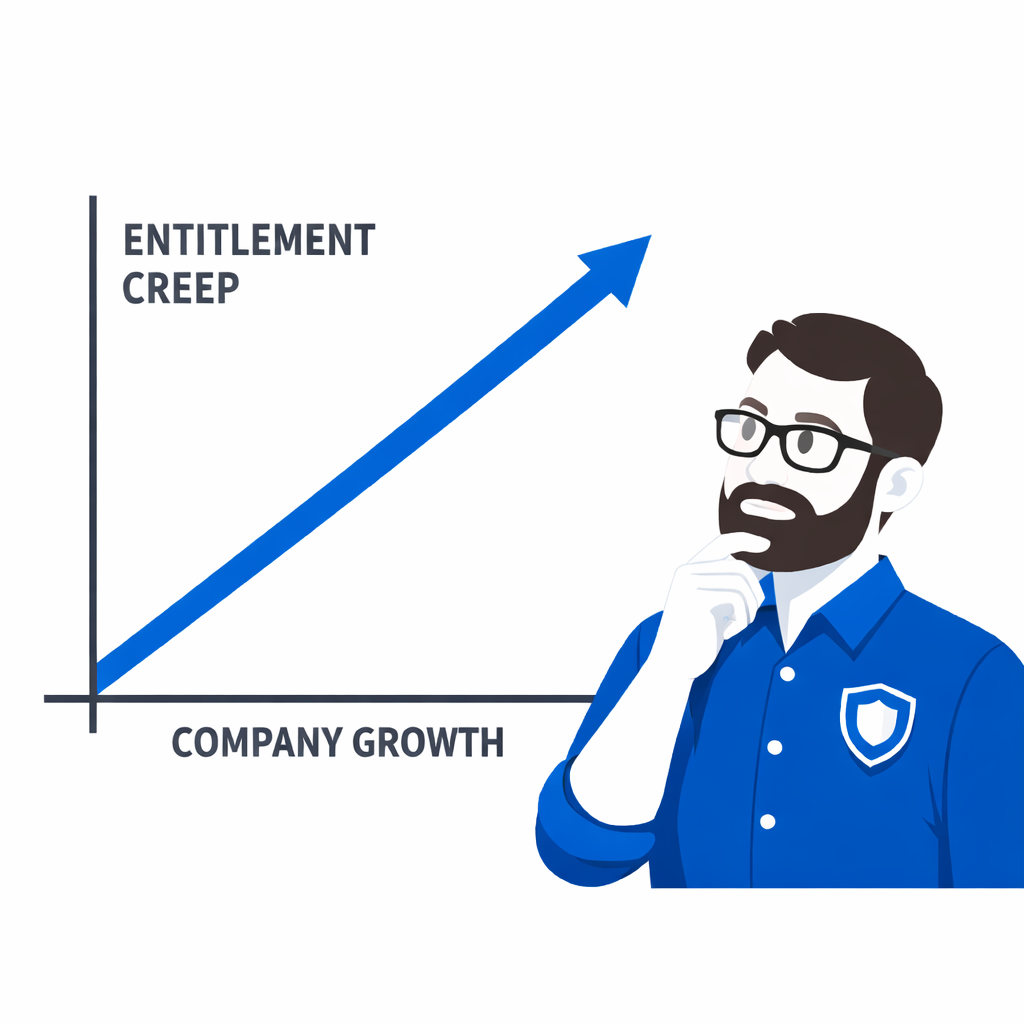
This means that traditional "always-on" access models create unnecessary risk exposure for 95-99% of the time, with access granted but not needed.
Quantifying access risk in dollar terms
Organizations are increasingly translating this time-based exposure into financial risk. By assigning a risk premium to each hour of unnecessary access, companies can calculate the actual cost of overprovisioned entitlements:
Risk Value = Hours of Unnecessary Access × Risk Premium per Hour
For example, if we conservatively estimate a risk premium of $1 per hour per account, a single user with 8,760 hours of unnecessary access represents $8,760 in annual risk exposure. Multiply this across hundreds or thousands of employees and the numbers become significant.
The multiplier effect of multiple accounts
The risk intensifies when we consider the reality of modern enterprise environments:
- Multiple accounts per user: Many employees have separate accounts for different SaaS applications and environments
- Service accounts: System-to-system communication requires additional accounts that often have elevated privileges
- Contractor accounts: External workers require access that is even more likely to be temporary
Each additional account represents another 8,760 hours of potential exposure. An organization with 1,000 employees averaging 3 accounts each faces over 26 million hours of annual access exposure—most of it unnecessary.
Just-in-time access: aligning access with actual usage
Just-in-time access fundamentally transforms this equation by providing access only when it's needed. With JIT:
- Users request access for specific timeframes
- Access is automatically revoked when the timeframe expires
- The default state becomes "no access" rather than "full access"
This approach can reduce exposure from 8,760 hours to the few hours actually needed—often representing a 99% reduction in risk exposure. Using our earlier calculation, this translates directly to a 99% reduction in dollar-denominated risk.
Data-driven JIT: moving beyond basic time restrictions
Advanced JIT implementations leverage usage data to make intelligent access decisions:
Actual usage patterns
By measuring actual entitlement usage—not just access rights—we can see the gap between provisioned access and genuine need. This data allows access policies to evolve based on real usage patterns rather than assumptions.
When displayed visually, most organizations are shocked to see how much of their entitlement time goes completely unused. As JIT is implemented, the gap between potential access hours and actual usage hours dramatically narrows.
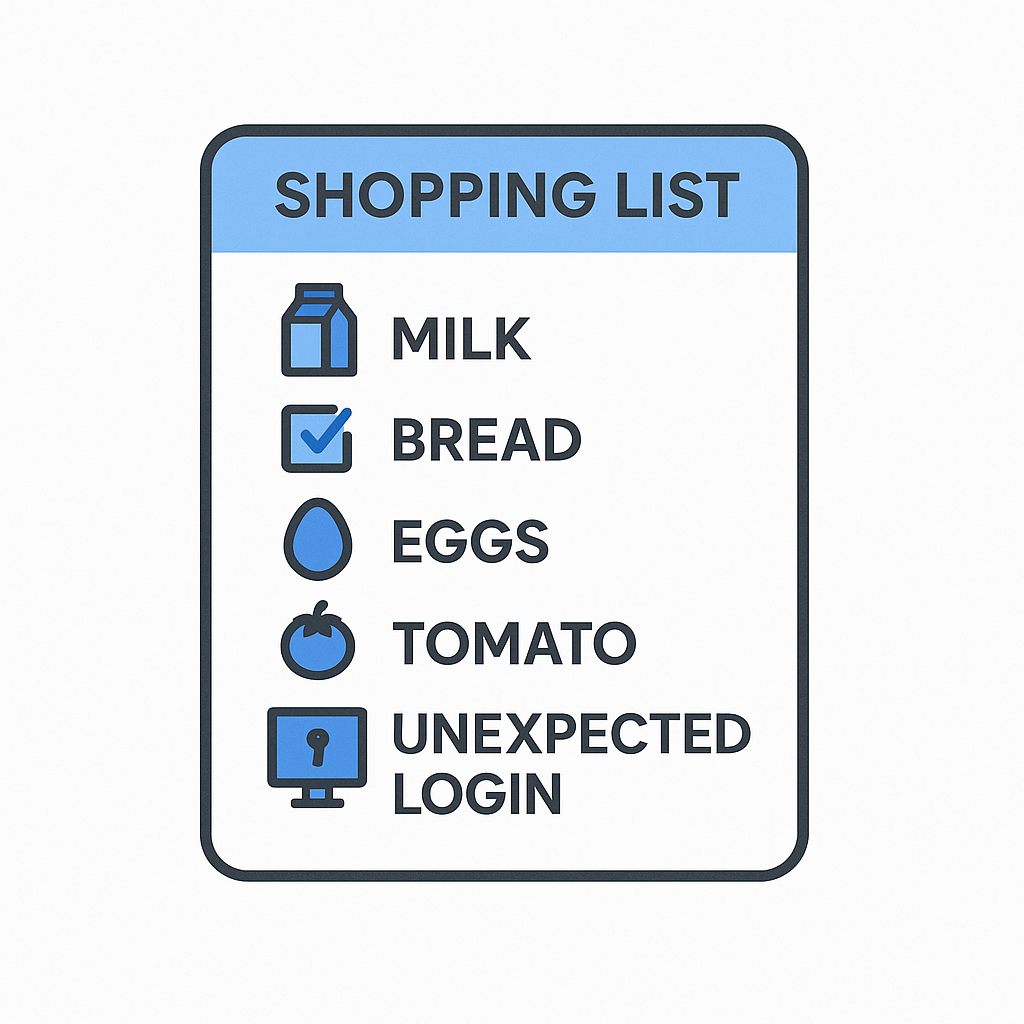
Contextual factors
Sophisticated JIT systems incorporate contextual information to further refine access decisions:
- On-call schedules: Automatically providing elevated access only during assigned on-call periods
- Peer comparison: Flagging when a user's entitlements significantly deviate from colleagues with similar roles
- Behavioral patterns: Learning individual usage patterns to identify anomalies that might indicate compromise
Measuring success: the convergence metric
A key indicator of effective JIT implementation is what I call the "access convergence ratio"—the percentage of provisioned access time that aligns with actual usage. The formula is simple:
Access Convergence Ratio = (Actual Usage Hours ÷ Provisioned Access Hours) × 100
Traditional environments typically show ratios below 5%, while mature JIT implementations can achieve ratios of 80%+ by dramatically reducing the denominator. This metric provides a clear, objective measure of progress in reducing unnecessary access exposure.
Conclusion
By shifting our perspective to view entitlements through the lens of time, we unlock new ways to measure, manage, and mitigate risk. Just-in-time access isn't merely a security enhancement—it's a fundamental rethinking of how access should work.
The most compelling aspect is that this approach doesn't require sacrificing user productivity. In fact, by building intelligence into the process—incorporating factors like on-call schedules, peer comparisons, and usage patterns—we can create systems that provide appropriate access exactly when needed while eliminating the vast expanses of unnecessary exposure that represent pure risk.
In today's threat landscape, organizations can no longer afford to leave sensitive resources accessible 24/7/365 when they're only used for a fraction of that time. Measuring and managing the time dimension of access is the next step in security risk reduction.