Discover cloud identity risks
Quickly find orphaned user accounts, service account misuse, and standing privileges across multiple cloud platforms
Revoke unused privileges
Review the usage of thousands of cloud permissions -- revoke all but what is needed for each human and AI agent
Adopt just-in-time access
Reach Zero Standing Privileges (ZSP) -- your teams self-provision access from Slack or Microsoft Teams and lose access soon after

Take the guesswork out of access management
Understand all of your privilege sprawl across cloud infrastructure and SaaS applications. Pinpoint the biggest concerns and revoke what isn't needed.

Review over privileged users
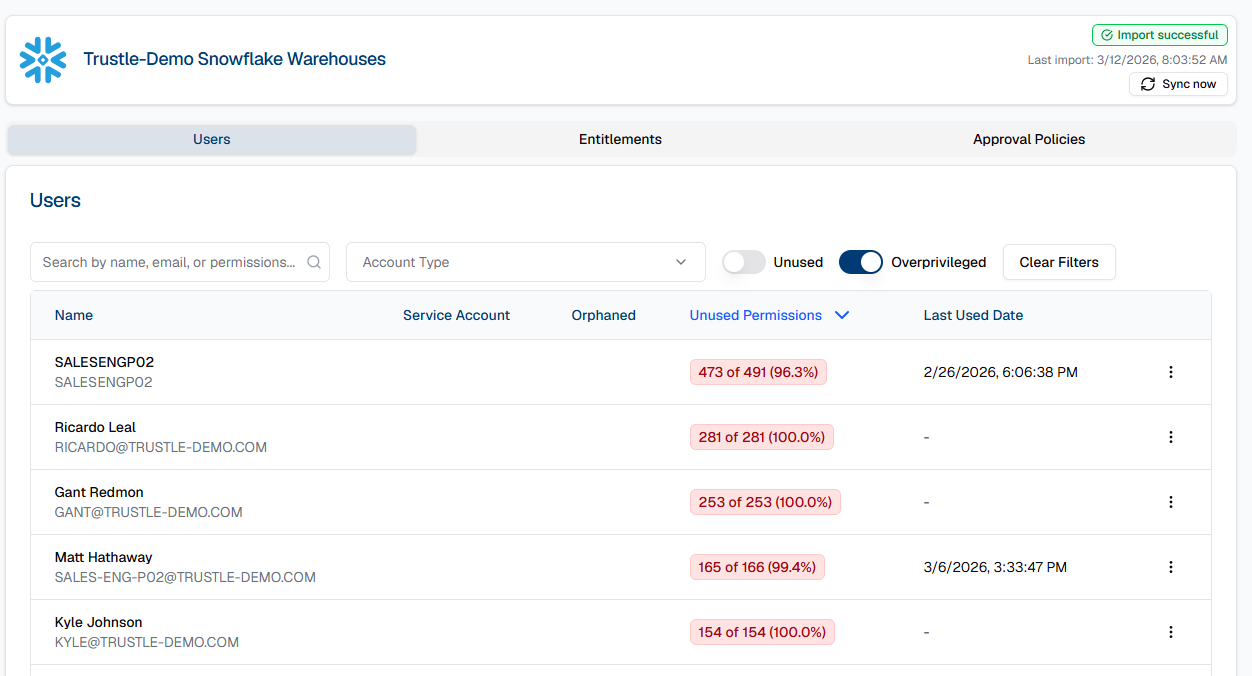
Fine-grained access control

Control all access from a single place
Provision new users and de-provision departing users across all of your environments and applications in moments.

Trustle Blog
Practical guidance on identity, access, and securing modern cloud environments
Don't fall behind the curve
Discover powerful features designed to simplify access management, track progress, and achieve frictionless JIT.