The audit doesn’t fail because we lack controls, it fails because we can’t show them
The elephant in the room usually arrives about 20 minutes into the audit. Someone on the call says, “We follow least privilege,” and the auditor nods politely, then asks the question that ruins everyone’s afternoon:
“Show me.”
Not our policy PDF. Not a Jira ticket where a manager typed “approved 👍”. We have to show them why the access was necessary, how we re-validated it, when we removed what wasn’t justified, and what stops privileges from becoming permanent—basically the classic Five W’s or elements of circumstance, part of the “seven circumstances” so beloved by my journalism tutor.
That’s what “prove least privilege” means in practice: a reproducible evidence chain. And if we’re running a cloud SOC or supporting one, this is where theory meets reality, because cloud permissions aren’t a tidy list. They’re a layered mess of roles, policies, groups, inherited rights, resource policies, conditions, and “temporary” exceptions that have outlived two mergers, organizational growth, and an agentic AI security revolution.
Least Privilege is a Control, Not A Buzzword
According to NIST, least privilege means allowing only the authorized accesses necessary to perform assigned tasks. But NIST also raises the bar with the part most organizations gloss over: periodic review of assigned privileges, and corrective action if the rationale can’t be revalidated.
PCI DSS v4.0 is even more direct. It doesn’t just want approvals, it expects us to review all user accounts and access privileges at least once every six months, ensure access remains appropriate for job function, address inappropriate access, and have management acknowledge the outcome.
And ISO 27001:2022 frames access as a lifecycle we must manage: provision, review, modify, and remove. Consistently, not occasionally.
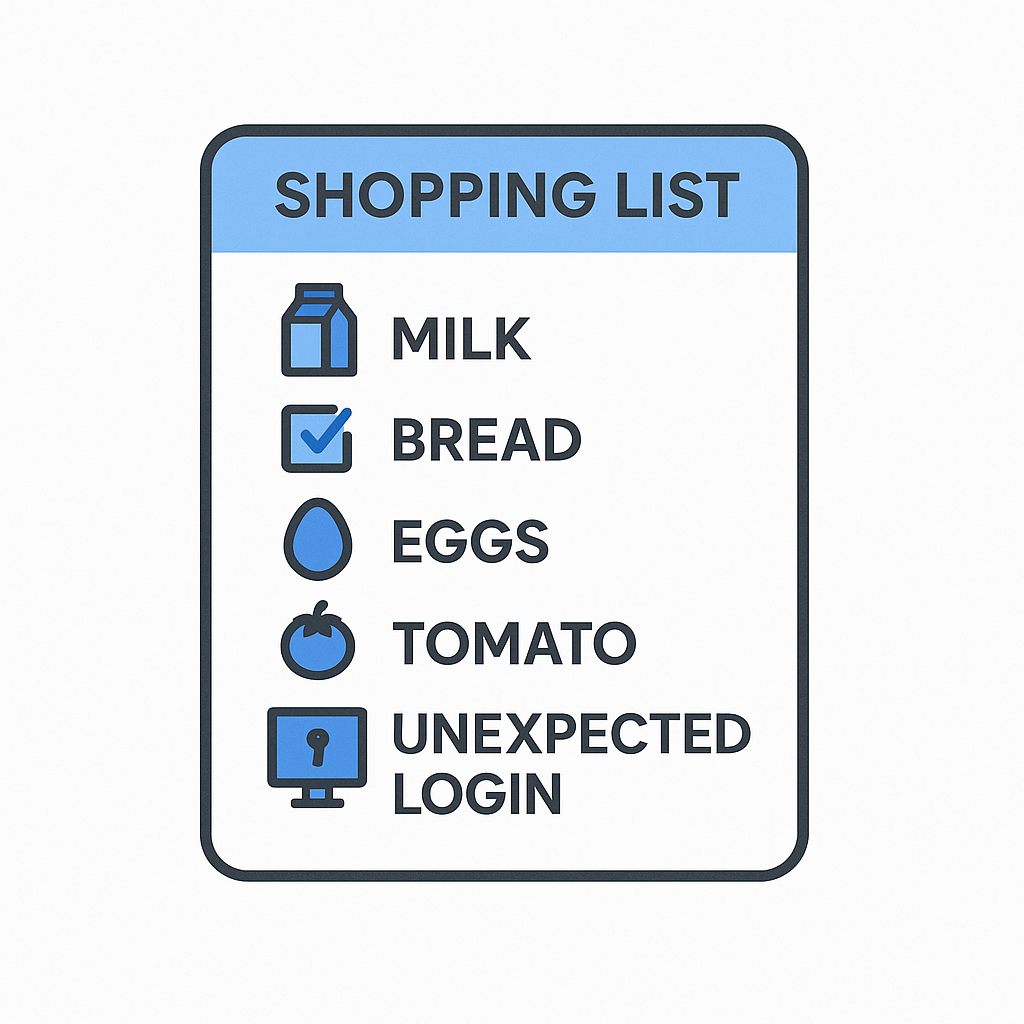
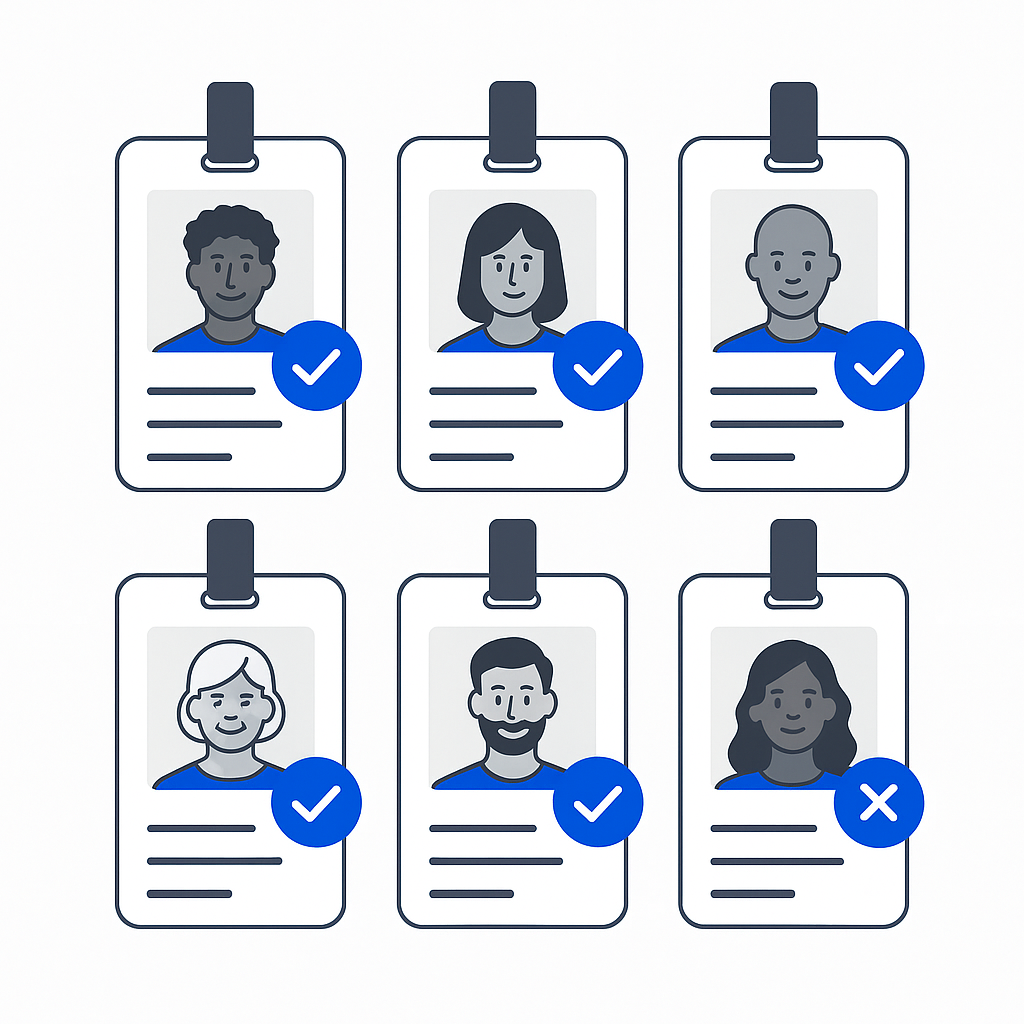
Remember when we’re in math class at school and we got penalized for not showing our work? Yeah, well, it’s kinda the same thing. If you want to prove least privilege, you need evidence in the following four categories (the Four E’s, if you like). These are the questions auditors are really asking, for human and non-human identities.
Evidence of Necessity: “Why Did This Person Need This?”
Approvals are not necessity. An auditor wants to see that access is granted because of a defined business need, tied to role, scope, and task, not because someone asked loudly enough in Slack.
Good evidence of necessity looks like:
- A role or function that maps to a permission set (“on-call SRE for production incidents”, not “engineering”).
- A clear boundary: which environments, which data types, which actions.
- For exceptions: documented justification and constraints (time window, scope, approver).
In cloud land, necessity falls apart when we can’t show effective access. If we’re reviewing a user’s “role assignments” but missing resource policies, inherited permissions, or group-based entitlements, we’re not proving anything. We’re guessing with confidence.
Consider this: Do we actually know, right now, what our agentic AI access is connecting to, and why? What legitimate and controlled permissions do our machine identities have, and how can we prove it?
Evidence of Review: “How Do You Know It’s Still Least Privilege Today?”
This is where a lot of teams get exposed. They have onboarding approvals. They have a folder of quarterly screenshots. What they don’t have is a review process that produces measurable change.
NIST explicitly calls out periodic privilege review to confirm the rationale remains valid, and to take corrective action when it doesn’t. PCI DSS v4.0 makes it testable: six-month reviews, documented results, and management acknowledgement.
To an auditor, a “review” that doesn’t lead to remediation is just a meeting with no coffee and extra steps. They want review evidence that holds up to scrutiny and ticks their boxes:
- Who reviewed what (system-generated scope, not hand-picked samples).
- What decisions were made (keep, reduce, remove).
- What changed afterwards (actual entitlement adjustments).
- A cadence you can defend (and repeat).
If we’re a GRC team, this matters because audits don’t care that we’re busy. They care that our access posture doesn’t drift while we are.
Evidence of Revocation: “Show Me You Removed Access”
Revocation is the moment of truth. Auditors want to see that over-privilege isn’t just identified, it’s eliminated. This can be triggered by the likes of joiner/mover/leaver events, failed or incomplete re-justification, and risk signals (unusual activity, policy violations).
The key, however, is the before-and-after. It’s the difference between:
“We reviewed Jane’s access and decided she didn’t need production write privileges.”
and
“On 12 March at 14:07 UTC, Jane’s Prod-Write-Role was removed. Here’s the log entry. Here’s her effective access before. Here’s her effective access after.”
If our evidence is “we told the app owner,” we’re betting our audit on someone else’s inbox hygiene. No, it’s not subtle, but removal is part of the control.
ISO 27001’s access-rights lifecycle language is useful here: access rights should be provisioned, reviewed, modified, and removed according to policy.
Evidence of Expiration: “What Stops Privilege From Becoming Permanent?”
Long-lived privilege is where least privilege goes to die. The fix isn’t “remind people to clean up.” The fix is designing access so it expires by default.
Auditors like time bounds because time bounds are measurable. If a privilege grant has a defined duration and auto-expiry, organizations can prove:
- When it started.
- When it ended.
- What was granted.
- Who approved it (if approvals are required)
- Whether it was renewed (and why)
This is also where GRC teams get a practical win: fewer standing privileges means fewer high-value targets sitting around waiting for credential theft to happen.
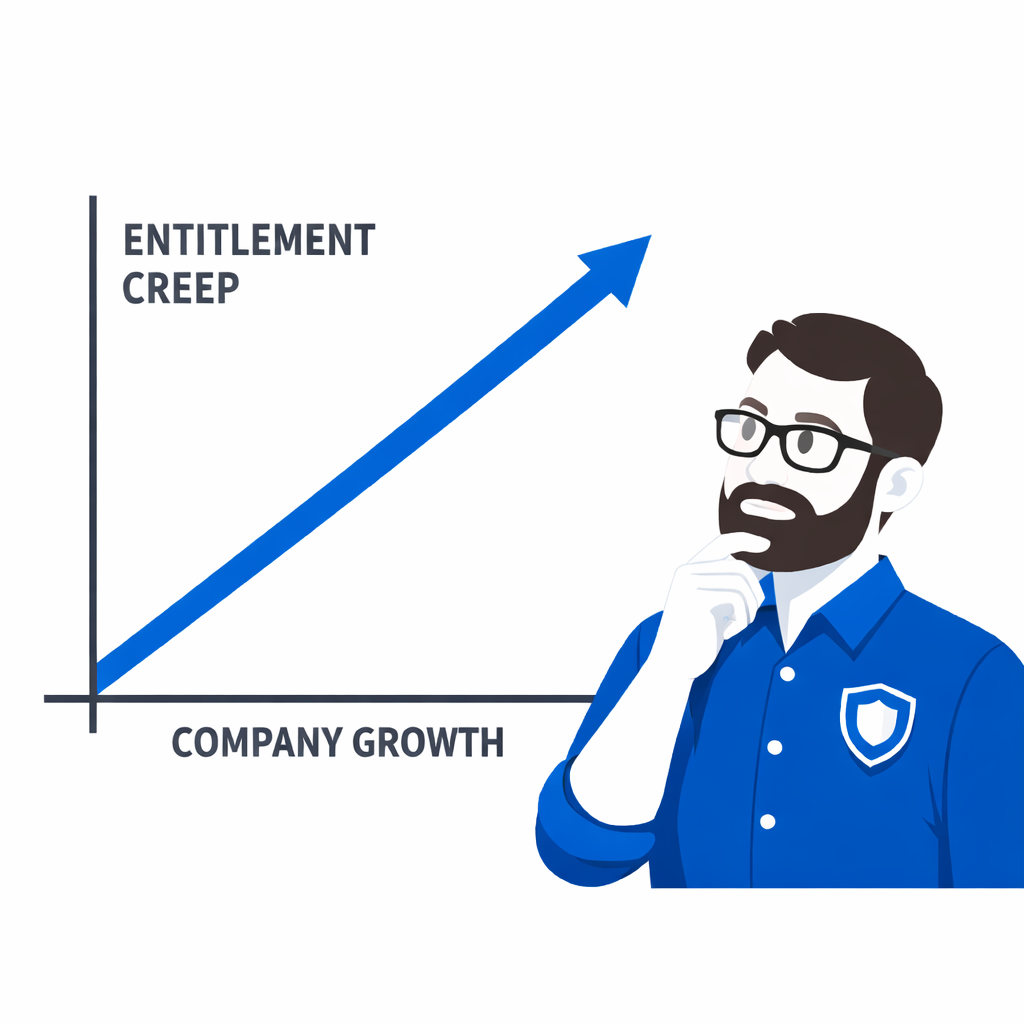
Why Most Organizations Can Show Approvals But Not Control
Approvals are a point-in-time artifact. Control is continuous.
When you hear a CISO say, “We’ve got least privilege,” the tell-tale audit follow-up is: “Can you reproduce it for any identity, any system, on any date?”
If we can’t generate that evidence chain on demand, we don’t really prove least privilege, we negotiate it.
Turning “We Think” Into “Here’s The Evidence”
The simplest way to explain what we do at Trustle isn’t “we do least privilege.”
It’s: we make it provable.
- Evidence-driven entitlement mapping gives security teams the effective-access baseline they need for necessity and review (without playing detective across three clouds and five identity stores).
- Automated policy enforcement turns review outcomes into action. Revocation and reduction that actually happens.
- Time-bound access and automated expiry make “expiration” a control organizations can demonstrate, not just some promise we make.
The audit goal isn’t to sound compliant. It’s to be able to answer “show me” without rummaging through tickets and replaying six-months of Microsoft Teams.
If our SOC can produce evidence of necessity, review, revocation, and expiration, on demand, audits stop being the elephant in the room and start looking like what they should be: a repeatable check that our controls work.